Ciphers, codes, and keys—plus reflections on how to encrypt sensitive developments in early American diplomacy—run through the papers of two generations in the Adams family’s saga of public service. So how did they use secrecy in statecraft?
Minister John Adams (1735-1826), working to secure peace with Britain after the American Revolution, battled through a number of different ciphers and codes (some “unintelligible,” he complained) when circulating news from the continent in the 1780’s. Though he was encouraged to employ the “secret language” of ciphers in private correspondence, John did so only sparingly, and his wife Abigail rejected the notion completely. “Thank you for your alphabetacall cipher tho I believe I shall never make use of it,” she wrote to code-maker James Lovell in 1780. “I hate a cipher of any kind and have been so much more used to deal in realities with those I love, that I should make a miserable proficiency in modes and figures. Besides my Friend is no adept in investigating ciphers and hates to be puzzled for a meaning.” Benjamin Franklin, glancing at the same Lovell cipher in Passy, ruefully acknowledged the need to veil his views but found the mechanism “too tedious for a whole Letter.” By contrast, Abigail’s eldest son met with greater success in making and breaking codes. John Quincy (1767-1848), busy finalizing the Treaty of Ghent, drew on Napoleonic-era innovations in cryptography to transmit news of his progress. Skimming through the Adams Papers’ “Ciphers and cipher keys” manuscript box recalls a republic where “Secret Journals” recorded official Congressional activity, and John Adams’s Alien and Sedition Acts came to redefine notions of citizenship, libel, and treason.
Early Americans employed a wide variety of ciphers and experimented with spycraft; scholars like Ralph E. Weber, David Kahn, Roger Kaplan, Simon Singh, and Russ Castronovo have charted different chapters of the narrative. Notably, the highly “individualistic” development of American cryptography within the eighteenth century’s “era of the black chambers,” had, as Kahn observed, “the informal, shirtsleeve quality of a pioneer barn-raising.” Colonial political culture played a major role in shaping how American citizens eluded or challenged surveillance. Military choices did, too. Loyalists and patriots alike grew accustomed to covert forms of communication—a practice that formed what Toby L. Ditz has called a culture rife with “secret selves”—in tavern meetings and committees of correspondence. Codes and ciphers circulated far beyond the reading public. Popular sentiments of independence, embedded in rebuses and other picture-word puzzles or satirical cartoons, carried the plaintext of political protest to the non-literate audience. Attempting professional espionage without a black chamber to guide them, early Americans favored dictionary/book ciphers and keyword/alphanumeric codes. Several pre-printed codesheets, or nomenclators, appear in the Adams Papers as evidence of the informal industry’s growth, with 600- to 1,700-element substitution cipher sets. Until the U.S. Department of State issued a codebook in 1867, these nomenclators formed the standard for early American diplomatic use. And, to further complicate modern understanding of these documents, encoders often used the terms “code” and “cipher” interchangeably—a good tip for archival research.
As part of the effort to preserve American neutrality, the fledgling diplomatic corps worked hard to moderate or obscure any observations that ran contrary to national policy. Success in foreign affairs, as secretary John Jay advised in 1787, relied on a blend of “perfect secrecy and immediate dispatch.” Fear of the fallout from intercepted letters ran high, and rightfully so. Thomas Boylston Adams, serving as John Quincy’s secretary at The Hague, took extra precautions in posting reports. When Thomas accidentally ripped open his brother’s mail before forwarding it, he hastened to reassure the Secretary of State that the contents were still safe. “I have taken the liberty to seal a scrip of paper across the place cut,” he wrote, “with two impressions of my Cypher, and hope these precautions may ensure the packet against a fresh violation, in its passage by the post for Paris.” Many well-educated civil servants like the Adams statesmen used shorthand to capture the events, trial notes, sermon reflections, and flights of philosophy that did not quite fit into the margins of their interleaved almanacs and commonplace books. But all of that casual proficiency did not mean that encoding practices were well-regulated, or even easy for the experienced reader to grasp. “I wish what I have put in Cypher may be tollerably correct, not having Time to examine it,” one American consul wrote.
In the spring of 1785, buoyed by the Anglo-American peace and new commercial treaties with the Netherlands and Prussia, Congress assigned foreign ministers to London and Paris: John Adams and Thomas Jefferson. Any news they might glean and share from Europe was precious. To do so, Jefferson developed what he called “Code No. 8,” a 1,700-element alphanumerical substitution cipher. First, Jefferson penned his letter and on a separate sheet of paper, wrote out the passage to encode with parenthetical marks. Then, either he or his secretary William Short inscribed the numbers. Thanks to our colleagues at The Papers of Thomas Jefferson and a review of the letterpress copies held at the Library of Congress, we know that in Jefferson’s Code No. 8, an apostrophe (’) following an element meant “make plural” or “add an s.” A caret (^) under the last numeral of the element doubled the last letter of the word or syllable. A prime stroke (ʹ)—straight, not curved like an apostrophe—following an element meant “make this verb past tense.” (At this point in research, I was very grateful for the London Rare Books School tutors who led us through several centuries’ worth of paleography in one week. Studying how people build, edit, and transmit written language was a vast research aid.)
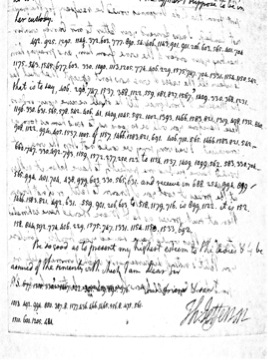
Back to 1785: John Adams, upon receiving and decoding the cipher, replied to the letter and used the code in the same way. Adams also kept a letterbook copy of most outgoing correspondence, scribbling “in Cypher” as a docket. At some point in April or May of 1785, Jefferson sent a cipher key to Adams, but it is no longer extant. Adams’s own copy of the key was imperfect—he wrote Jefferson at one point to point out a copyist’s error—and it is interesting to note that minus his regular secretary William Stephens Smith, it was the American statesman’s daughter Abigail 2d (“Nabby”) who accomplished much of the ciphering and deciphering on his behalf. “A Letter from Mr. Jefferson, came by the Post to day,” Nabby wrote to brother John Quincy, sharing encrypted news of the Diamond Necklace Affair. “He writes in sypher, and when there is nobody elce to desyper I have the agreable task. I am paid perhaps for my trouble by knowing what is written.” John Adams and Thomas Jefferson selectively used Code No. 8 to exchange updates on the quasi-“Germanic” diplomacy of George III, the stir of Parisian political networks, the effort to free sailors impressed and enslaved by Barbary pirates, and Adams’s diligent work to press the British ministry on evacuating frontier posts and settling prewar debts. (You can read all about it in The Papers of John Adams, vol.17).
To a degree, cryptography professionalized the fledgling diplomatic corps. The American consul of 1796, for example, departed with letters of credence and credit, but awaited coded instructions and a cipher key once at his post—this was the case for young John Quincy Adams when he left for The Hague that spring. For a consul eager to report, and impatient with the standard six-week wait for mail, the alternative was to invent his own cipher. John Quincy did so to communicate with his predecessor, William Vans Murray. Murray was a skilled encoder and a cautionary tale: the problem of intercepted mail had damaged his own standing among foreign colleagues. His commonplace book shows a number of ciphers, including an 11-element picture code, where □ is France, Δ is Great Britain, and ooo means “combined powers.” John Quincy’s interest in handwriting as a symbol system, evident in his lifelong study of foreign languages, made him an agile tutor of pre-printed cipher mechanics. He was especially taken with sliding lock-and-key systems. Writing home in his “hieroglyphics,” John Quincy sent encrypted reports of British famine, eruptions within the French Directorate, and the democratic establishment of the Batavian Republic. Words like “manufacture,” “Jacobin,” or “Law of Nations”—as he thought—required a secret language for masked dispatches. As linguistic artifacts of an era transformed by federal enterprise, national growth, and postal service, the Adams Papers ciphers and keys form a unique grammar of early American diplomacy.



Pingback: History A'la Carte 12-4-14 - Random Bits of Fascination